“Before you breach a system, understand the terrain it lives on.“
Web applications live on networks. So do vulnerabilities. And a hacker who doesn’t understand the network layer is like a thief who can pick locks but doesn’t know how doors work.
Network analysis isn’t a checkbox. It’s reconnaissance, surveillance, and intel all in one.
For a Ethical hacker, it’s not just about packets — it’s about patterns, exposure, and assumptions made by sysadmins that no one ever questioned… until you showed up.
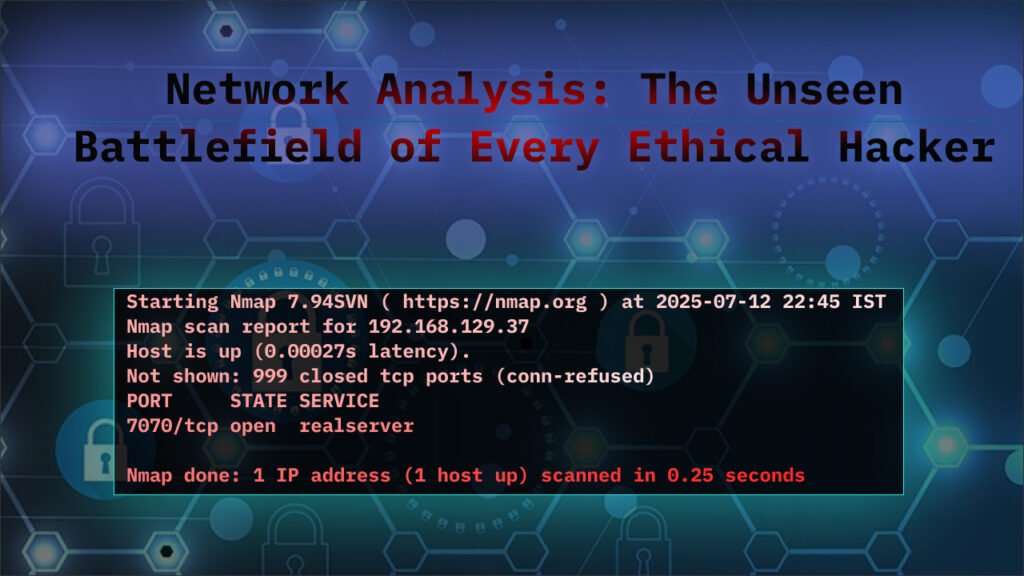
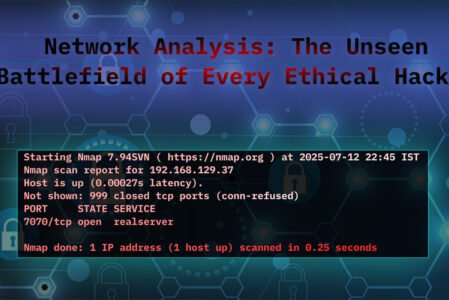
Network Scanning: Mapping the Terrain
Most networks are built like cities — open avenues, guarded gates, dark alleys. Scanning isn’t about lighting up everything. It’s about asking subtle, well-formed questions.
Think like this:
- Which services are exposed to the outside?
- What ports are listening internally but not externally?
- Is this port showing different behavior from one IP to another?
This is not a port sweep — it’s a behavioral analysis.
You’re not just listing IPs; you’re imagining the layout. You fire up a scan with -sS for stealth, checking for live hosts, and ask, “What’s hiding here?” Maybe you spot an old server on 192.168.1.10 that shouldn’t be online. To level up, you chain this with port enumeration, finding an open service that leads to a misconfigured admin panel. It’s about seeing the big picture and planning your next move.
Use stealth scans, fragmented packets, randomized timing. Make your presence known without actually being seen
Port & Service Enumeration: Knocking on Doors
A service running on port 80 isn’t just a web server. It’s a fingerprint, a context clue.
The goal is not just to find “what” is open, but:
- What version is running?
- How was it configured?
- Is it default?
- Has it been patched?
Take this further:
- SSH on port 22? Try banner grabbing — maybe it’s an outdated OpenSSH.
- MySQL open on 3306? Try connecting anonymously or using default creds.
- SMTP on 25? Test for open relay.
You’re a burglar casing a joint, wondering, “What’s unlocked, and what’s old?” You spot port 445 (SMB) and dig deeper with smbclient to check for outdated Windows shares. The goal? Find version numbers—like an ancient Samba 3.0—that hint at known bugs. Chain this with a vulnerability scan, and you might unlock a remote code execution path, turning a simple port into a bounty winner.
Packet Sniffing: Eavesdropping on the Conversation
Sniffing isn’t passive — it’s interpretation.
When you capture packets, you’re not just logging bytes. You’re seeing how the application breathes.
What to watch for:
- Plaintext credentials
- Misconfigured headers (e.g., leaking internal IPs)
- Suspicious traffic patterns (e.g., high-frequency internal requests)
- Forgotten protocols (like NetBIOS, Telnet)
Tools like tcpdump and Wireshark give you visibility. But it’s your human pattern recognition that turns visibility into exploitation.
Even encrypted traffic can be valuable. Look at the SNI, metadata, timing. Even encrypted packets have shape.
Traffic Analysis: Reading Between the Lines
Networks leak intent when you know how to watch.
What is the server doing during off hours? What’s the DNS request volume like? Are there periodic connections to strange IPs?
You’re a traffic cop, wondering, “What’s out of place here?” You notice a server sending megabytes to an unknown IP at 3 a.m.—possible data exfiltration. With tools like Zeek, you track the source and destination, asking, “Is this normal?”.
Use traffic analysis to map out privilege levels and potential pivots.
ARP/DNS Spoofing Simulation: Playing the Trickster
Simulating internal network behavior can show you where security falls apart.
DNS spoofing isn’t just a LAN attack — it exposes how much the app relies on DNS assumptions:
Can you override DNS responses via a local proxy?
Can you abuse SSRF to trigger DNS-based data exfiltration?
Using tools like BetterCAP, you send spoofed ARP packets to hijack traffic, or tweak DNS responses to point to a fake site. The thrill is in seeing if the network catches it. Chain this with packet sniffing to capture redirected credentials, and you’ve got a solid proof-of-concept to show a client’s security gaps.
Host Discovery: Finding the Hidden Players
Not all devices respond to pings. Not all hosts expose their presence willingly. Real host discovery is probing behavior, not ping responses.
Test:
- Reverse DNS sweeps
- Passive DNS logs
- NetBIOS/SMB enumeration
- ICMP type 13/17 requests (timestamp/netmask)
- Unexpected ports like SNMP, SSDP
You’re a tracker in the wild, asking, “Who else is out there?” You ping a range like 10.0.0.0/24 and spot a device at 10.0.0.99 that’s not in the IT inventory—maybe an old printer with open ports. Chain this with port scanning to find vulnerabilities, and you might uncover a forgotten device ripe for exploitation.
Think beyond live hosts. Think live services, internal-only interfaces, accidentally public test VMs.
Protocol Inspection: Decoding the Language
Every protocol has layers — and assumptions. And where there are assumptions, there are bugs.
Don’t just look at HTTP. Inspect:
- FTP (does it allow anonymous login?)
- SMB (can you list shares?)
- DNS (does it allow recursion or AXFR?)
- TLS (weak ciphers, self-signed certs?)
You’re a linguist cracking a code, wondering, “What’s this protocol saying?” You spot an FTP session with plaintext passwords or an HTTP request leaking API keys.
Inspect how TLS negotiation happens, analyze fallback behaviors, observe keep-alive misuse, check for inconsistent responses based on origin IP.
Network Analysis is more than a skill—it’s a journey into the heart of how data moves. For ethical hackers, it’s about outsmarting the system, protecting the digital world, and maybe cashing in on a smart find. By mastering scanning, sniffing, and spoofing, and tying it all together with a hacker’s gut, you’re not just analyzing—you’re telling a story of discovery.
Case Study: TCP Hijacking via Sequence Number Leakage Over NAT-Enabled Wi‑Fi
Network Analysis: The Unseen Battlefield of Every Ethical Hacker